TCP SYN flood - USC/ISI
Overview
This exercise demonstrates a well-known denial-of-service attack, called TCP SYN flood. Students will be able to create a real attack using DETER tools, and to observe its effect on legitimate traffic. Afterwards, they will be asked to apply a known defense against SYN flood known as SYN cookies, repeat the attack and observe the protection.This exercise helps students learn the following concepts: (1) How TCP/IP works and how its design can be misused for attacks, (2) How easy it is to perpetrate a DoS attack, with fully legitimate traffic and at a low rate, (3) How easy it is to protect machines from this type of attacks via built-in OS mechanisms. Additionally, extra credit questions improve a student's understanding of how networks and TCP/IP work.
Required Reading
All students should have completed an introductory networking course with grade B or better.
- Short summary of SYN flood attack on Wikipedia
- SYN flood attacks in the Internet Denial of Service book (optional reading)
- SYN cookie overview
- Tcpdump's man page
Introduction
Denial of service attacks deny service to legitimate clients by tying up resources at the server with a flood of legiitmate-looking service requests or junk traffic. Before proceeding to the assignment instructions make sure that you understand how TCP SYN flood attack works, which resource it ties up and how, and how syncookies help mitigate this attack.Assignment Instructions
Setup
- If you don't have an account, follow the instructions in the introduction to DeterLab document.
- Log into DeterLab
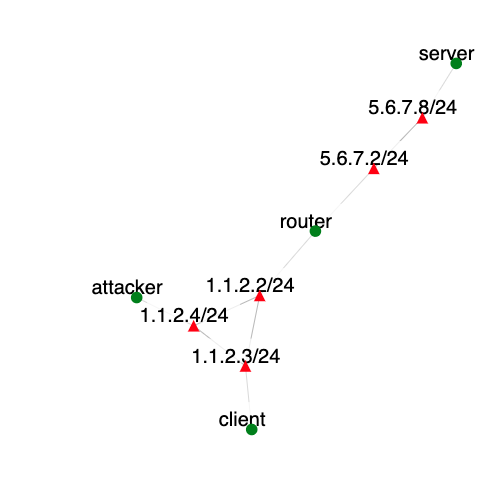
- Create an instance of this exercise by following the instructions here, using synflood as Lab name. Your topology will look like below:
 .
.
- After setting up the lab, access your nodes.
Tasks
Generating legitimate traffic
Create a Web traffic stream between the client and the server nodes by writing a script at the client that each second gets index.html from the server. You can for example write this script using bash and curl.
Turning off SYN cookies
SYN cookies are often on by default in Linux and FreeBSD. To check if they are on do the following on server node:sudo sysctl net.ipv4.tcp_syncookiesIf you see 1 as the result, SYN cookies must be set to zero for the demo to work. Type the following on the server machine:
sudo sysctl -w net.ipv4.tcp_syncookies=0 sudo sysctl -w net.ipv4.tcp_max_syn_backlog=10000Verify that SYN cookies are now off by typing on the server machine:
sudo sysctl net.ipv4.tcp_syncookies
Generating attack traffic
Create a SYN flood between the attacker and the server nodes, using the Flooder tool. You can type "flooder" on the attacker node's command line to get a man page for the tool. Examples at this page show how to write a command to send a flood of SYN packets. Make sure to spoof within 1.1.2.0 range (use mask 255.255.255.0).
Collecting statistics
You will now collect tcpdump statistics on client machine with and without syncookies, calculate connection duration and draw graphs of connection duration on y-axis and connection start time on x-axis. Perform the following steps:- Stop all traffic by stopping your legitimate client's script and flooder.
- Start tcpdump on the
client ip route get 5.6.7.8
You should see something like this as a result:5.6.7.8 via 1.1.2.2 dev eth2 src 1.1.2.3 cache mtu 1500 advmss 1460 metric 10 64Thus the interface name leading to 5.6.7.8 is eth2. To see the traffic flowing type:sudo tcpdump -nn -i eth2
then generate some traffic, restart your legitimate client code. You will need to discover proper tcpdump options to see only IP traffic and to save recorded traffic into a file. Start tcpdump with these options. -
Using a stopwatch perform the following scenario:
- Start legitimate traffic
- After 30 seconds start the attack
- After 120 seconds stop the attack
- After 30 seconds stop the legitimate traffic
- Stop the tcpdump on the client and save the file
- Turn the SYN cookies on and repeat the above steps.
- Using the recorded traffic files and tcpdump to read them, process the output and calculate connection duration for each TCP connection seen in the files. Connection duration is the difference between the time of the first SYN and of the ACK following a FIN-ACK (or between the first SYN and the first RESET) on a connection. Recall what uniquely identifies a TCP connection, i.e. how to detect packets that belong to the same connection? If a connection did not end with a FIN or a RST, assign to it the duration of 200 s.
What can go wrong
- Attack is ineffective. Check that you are sending SYN packets (use tcpdump to verify) and that they are going to port 80. Also check that they are using spoofed source address. Finally, check that the volume is large enough (e.g., 100 or more per second).
Extra Credit
There are two extra-credit questions:- Remove spoofing from the attack. Repeat the exercise without SYN cookies and observe and explain the effect. What happens? Can you explain why this happens? For hints run a tcpdump on the server node and look for traffic patterns. Can you modify the attack so that it is effective without spoofing and how would you do this?
Submission Instructions
You should submit a Word document with the following items (label each section):- Explanation how the TCP SYN flood attack works.
- Explanation how SYN cookies work to prevent denial-of-service effect from SYN flood attack
- Your legitimate client script
- Your attack command (for flooder)
- The connecton duration graphs you drew in task 5 (one with SYN cookies, one without SYN cookies). Indicate on the graphs using vertical lines or arrows the start and the end of the attack.
- Explanation what happens in each case. Is the attack effective? How can you tell this from the graphs?
- Answers to extra credit questions if any.