CCTF: Resilient Server - USC/ISI
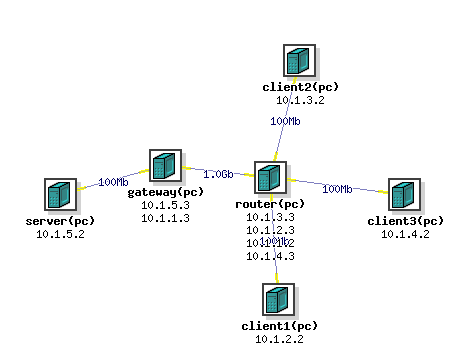
OverviewThis exercise lets students practice monitoring network for denial-of-service attacks and devising appropriate actions. Students will be divided into 3-4 person teams. Each team will play the defender role (Blue team) for their own system and the attacker role (Red team) for another team's system. Each network in the exercise will consist of six machines - a server and a gateway machine under the control of the Blue Team, three client machines under the control of the Red Team and a router machine that neither team controls. Links between clients and the router and the link between the gateway and the server are 100 Mbps. The link between the gateway and the router is 1 Gbps. This allows the clients to attempt to create DoS conditions by flooding the link between the gateway and the server. The network for the exercise is shown below and the NS file for it resides at /share/education/ResilientServerGamified_USC/cctf.ns.
Blue Team TasksThis team will control the server and the gateway machine, connected by 100 Mbps link. The server is a classical LAMP server, and it is seeded by 10 static Web pages. The Blue team should develop a monitoring program for the gateway machine and for the server so that they can quickly spot if the Red team launches denial-of-service and so that they can defend from it. One way to defend from it is to implement some filtering at the gateway machine via iptables. Blue team should be ready to implement filtering on the fly but they should develop a sophisticated monitoring program that helps them quickly figure out what to filter. The Blue team can also modify Apache's configuration and code to make the server more resilient to some attacks, or they can craft packets to end connections that behave suspiciously (e.g., TCP RST).
Make sure you understand how iptables command works before you use it as you may cut off your access to a given machine in DeterLab if you filter out some specific traffic to/from it, e.g., all outgoing traffic. The only way to recover from this is to reboot the machine using Web portal for DeterLab. Click on your Experiment, then click on the machine's name in the Node List (e.g., pc133) and then choose "Reboot node" from the top left menu. It usually takes 5-10 minutes for the machine to come up again.
The goal of the Blue team is to keep the server up and running. When the server gets attacked, the Blue team should strive to bring it back up quickly (if it is down) and to install filters to get rid of attack traffic. When developing and practicing swap in an experiment using /share/education/ResilientServerGamified_USC/cctf.ns file, and then run on users machine: perl /share/education/ResilientServerGamified_USC/start.pl expName projNameThis will lead to the identical setup as the one during CTF exercise. Assumptions and RequirementsYou can borrow code from online sources but you need to understand what it does and how. MilestonesHere are some milestones that your team must reach BEFORE the exercise.
Red Team TasksThe Red Team will have control over two out of the three client machines. Red Team can discover which client machines are available to host an attack by trying to log into each machine. The third machine is a legitimate client. Attack machines can act as legitimate machines some times and attack other times. Automated client software runs on all client machines. This sofware runs automatically to generate at most 1 request per second for one out of 10 static Web pages at the server node.The goal of the Red Team is to make the server unable to serve its legitimate client, either through compromise or through denial of service. Any attack is allowed, not just denial of service, even breaking Blue team's passwords. When developing and practicing swap in an experiment using /share/education/ResilientServerGamified_USC/cctf.ns file, and then run on users machine: perl /share/education/ResilientServerGamified_USC/start.pl expName projNameThis will lead to the identical setup as the one during CTF exercise. You can also use Deterlab's Flooder tool, which will be automatically installed on attack machines (type flooder to activate it), to send attack traffic. For more information about this tool see man page. Assumptions and RequirementsYou can borrow code from online sources but you need to understand what it does and how. MilestonesHere are some milestones that your team must reach BEFORE the exercise.
ScoringThe Blue Team receives a point for each legitimate client's request that the server processes and responds to within 500 ms. Red Team gets the point otherwise.Exercise DynamicsTeams will need to simultaneously act as Blue Team and Red Team throughout the exercise. We will then have a post-mortem discussion and selection of a winning team.GradingEach team member will be graded based on their contribution to the team effort, not based on the team's performance. After the exercise each team member will submit a report containing the list of contributions they made to the team effort - e.g., modules that they coded, testing and setup they performed, etc. All team members must sign each report. Reports will be delivered to the instructor in class. The grades will be assigned based on the report.Useful LinksYou can use any programming language you like for any part of your assignment.
|